Knowledge Base - SMAOT UICC: (2G XOR) Quick Guide
Let's get started!
- Start Card ADMIN by choosing Start > Programs > Gemalto > CardAdmin>CardAdmin.
- Have a 2G card from Smartjac ready; Do not punch the SIM card out of the plastic card as it needs to be in CR80 format to be entered in smart card reader.
Insert your 2G card in the smart card reader
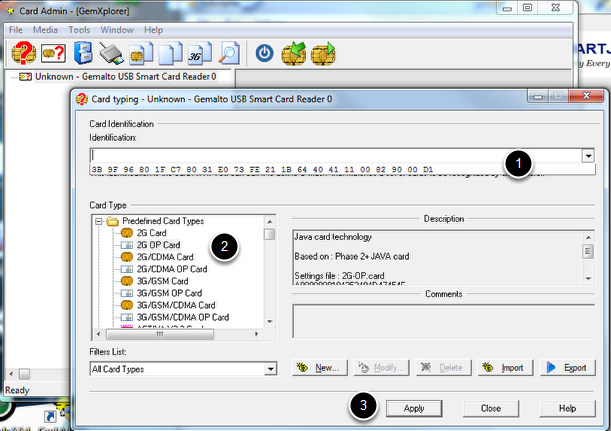
The first time the card is inserted in the card reader, Card Admin will not recognize the Card ID (the ATR signature from the card), so you'll need to select the ID and a correct predefined Card Type.
- Click on the pull-down menu and select the ATR
- Select "2G OP Card" from the Predefined Card Types
- Click on "Apply"
If you accidentally chose the wrong card type, please look a this article on how to change it.
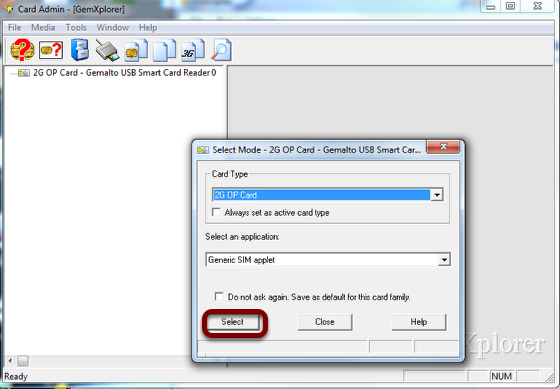
Select Mode window
Leave defaults and Click "Select"
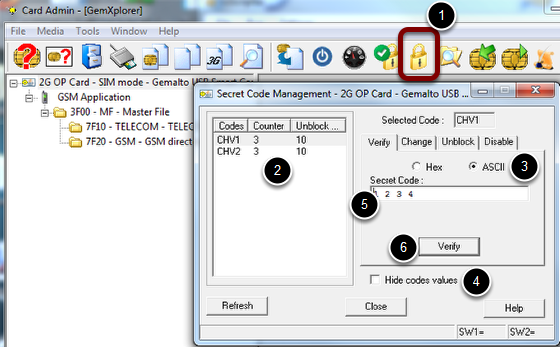
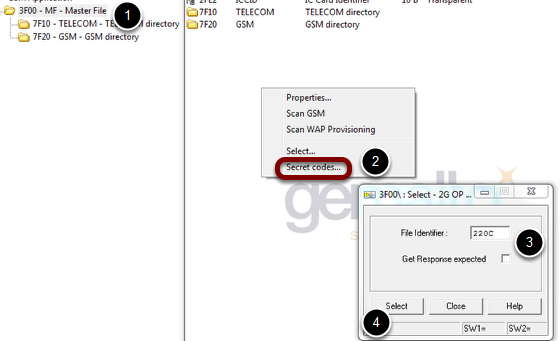
Verifying Secret Codes
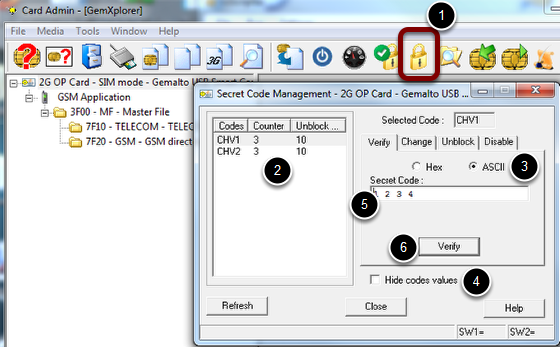
CHV1: 1234
CHV2: 5678
In order to view and edit files on the SIM card you'll need to verify the secret codes. Best practice is to verify them all at once before you start browsing the card and open files. The secret codes for this particular card can be found here.
The CHV / PIN or ADM secret codes are often required to use a command on a file (for example, Read, Update). The secret code to be verified for a given command is specified as an access condition when the file is first created.
To verify a secret code:
- Click on the Secret Codes icon on the top menu bar / or right click on the Master File (MF)
- Select the code to be verified in the list box.
- Select to verify the code in Hex or ASCII.
- Check the Hide codes values box if you want to mask the code values as “*”. If you want the code values to show, leave this box unchecked.
Note: If you have checked this box, enter the value carefully as an incorrect value will decrement the ratification counter of the secret code.
6. Enter the code value in the Secret Codes box and click Verify. The result and the corresponding status words are displayed in the status bar below.
Note:
For all cards, if you specify an incorrect value for the secret code, the Counter (ratification counter (Counter assigned to each CHV and ADM code in the card. It records the number of consecutive times the code has been incorrectly entered. If the ratification counter reaches 0 after a pre-determined number of attempts (chosen when the secret code is first created), the secret code is "blocked". If the secret code is entered correctly before it is blocked, the ratification counter is reset to its initial value, otherwise it must be unblocked using the Unblock CHV command. The purpose of the ratification counter is to prevent exhaustive secret code attacks.)) is decremented. If the Counter reaches 0, the card is blocked. In this case, select the Unblock tab.
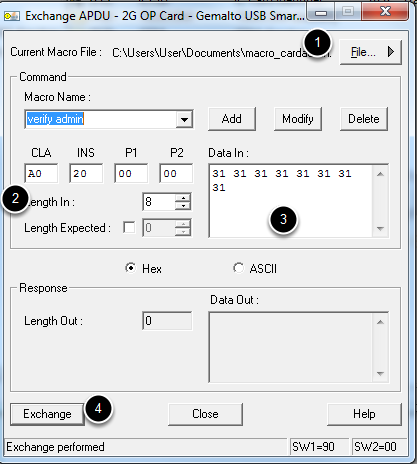
Verifying ADM code using APDU command
As these cards are non-gemalto cards, and as the commands to verify Admin codes are different between different suppliers of SIM cards, we'll need to verify ADM codes by sending a specific APDU command.
- Click on the "Exchange APDU..." button on the top-menu bar.
Verify ADM code on 2G card
- APDU commands can be saved in a Macro file. If necessary, create a new Macro file to store your APDU commands. This way you don't need to enter the APDU command manually everytime. After entering all APDU data you just add a new command to the file by entering a name and then click "Add".
- Enter APDU command A0200000 08 as showed in the screenshot above.
- Enter the Admin code 3131313131313131 in the Data in field.
- Click on the "Exchange" button
Make sure you got SW1=90 SW2=00 response from the exchange. (Success)
That's it. You have now succesfully verified the ADM code and you can proceed with editing files (EF's).
Personalisation sample - Editing some mandatory files
We will proceed by editing some of the files necessary to have a functional SIM card:
- Ki
- ACC
- IMSI
Putting the Authentication Key (Ki)
On the Smartjac 2G cards the authentication key is stored under MF / EF_220C
The Card Admin scans some predefined ranges and for that reason some files can not be seen unless you specifically select them.
- Click on 3F00 - MF - Master File
- Right-click on the right panel and select "Select..." on the pop-up menu
- Enter 220C in the File Identifier
- Click "Select"
- Close the Select window
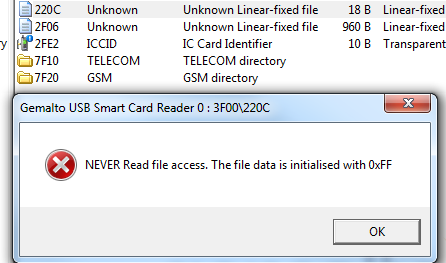
Open the file that stores the Ki key: 220C
- Double-click on 220C to open it
- A warning appears that the file is non-readable because of Access rights settings on that file preventing you to read the data in the file. This is ok and is as it should be for security reasons. Click on OK button.
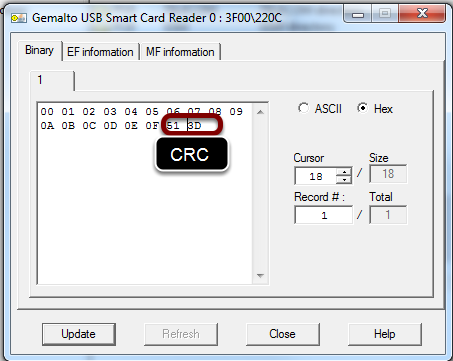
Setting the Ki
Enter the value of the Ki you want to use. The Ki is 16 bytes and the 2 last bytes are the CRC checksum.
How to calculate this checksum is explained in the Appendix here.
In the case of Ki being 000102030405060708090A0B0C0D0E0F the checksum is 513D
Click on "Update" button
Click on "Close" button
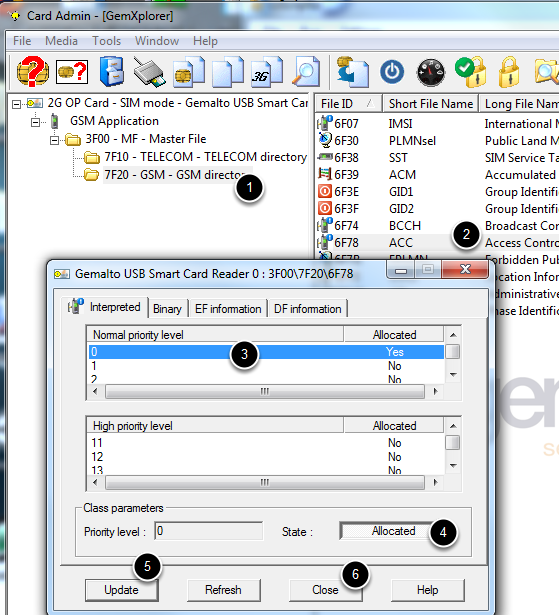
Set ACC
Each mobile belongs to one out of ten randomly allocated mobile populations, defined as Access Classes 0 to 9. Moreover, some mobiles may be members of one or more out of 5 special categories (Access Classes 11 to 15). Both these access classes are stored in the SIM.
If the mobile belongs to at least one access class allowed by the network, it can make calls. Otherwise all access attempts will be barred. So you need to set a value in this file. If you don't know, just set 00 01 (Normal priority level 0 allocated)
6F 78h, Access Control Class, is a transparent file containing the mobile’s random access class and possibly a special access class.
- Select the DF: 7F20 - GSM - GSM directory and on the panel to the right you will find the EF_6F78 file holding the ACC value.
- Double click on ACC
- Select first line (0)
- Click on "Allocated"
- Click on "Update" button
- Click on "Close" button
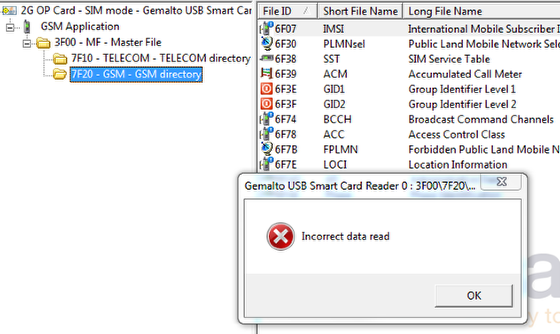
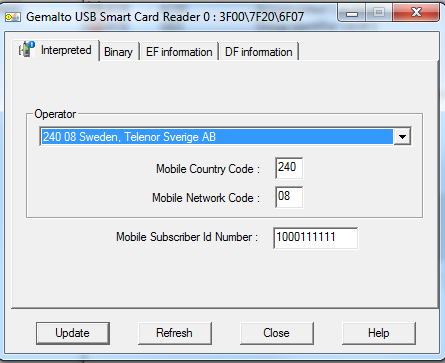
Set IMSI
- Select the DF: 7F20 - GSM - GSM directory and on the panel to the right you will find the EF_6F07 file holding the IMSI value.
- Double click on IMSI
- If the SIM card is "non-personalized" (i.e. only have some default or empty values) , you will get an "Incorrect data read" error. This is OK. Just click "OK" button.
Enter IMSI data
Enter MCC, MNC and Subscriber number and click "Update" button.
Click "Close" button
Details
Created : 2016-06-22 16:31:03, Last Modified : 2017-06-15 13:49:36
Access Control
Techniques and solutions to grant or deny access to a given user for a given digital service. Consumers are very familiar with Username/Password as a basic access control technique for popular web services such as web mails or eMerchants web sites. Security sensitive services such as Payment or eGov are often deploying more robust access control techniques, usually relying on Secure Elements, Smart Cards being one example.
Card Admin
Gemalto Telecom Card Admin tool is a tool to edit SIM & UICC cards. Card Admin provides all the necessary fundamentals to FULLY (Proprietary files, Proprietary commands etc.) administrate any 2G, 3G, LTE and CDMA card (Gemalto & Competition).
Module
The unit formed of a chip and a contact plate.
SMAOT
Smartjac OT series of UICC / SIM cards ranging from 2G SIM cards with XOR support, to advanced multi-application LTE UICC cards with Milenage support, NFC, USIM, ISIM and CSIM.
UICC
A high capacity smart card used in mobile terminals for GSM, UMTS/3G and now 4G/LTE networks.
Click for more info
Edge
A pre-3G digital mobile phone technology allowing improved data transmission rates.
Java
A network oriented programming language invented by Sun Microsystems and specificallt designed so that programs can be safely downloaded to remote devices.
HTTP
Hyper Text Transfer Protocol. A client-server communication protocol developed for World Wide Web. See IETF RFC2616, www.ietf.org.
IMSI
International Mobile Subscriber Identity. A unique number associated with each mobile phone user. It is stored in the SIM inside the phone and is sent by the phone to the network. It is primarily intended for obtaining information on the use of the Public Land Mobile Network (PLMN) by subscribers. It is also used for other functions such as to compute the Paging Occasions (PO) in LTE. See 3GPP TS22.016 and TS23.003.
SIM
A subscriber identity module or subscriber identification module (SIM) is an integrated circuit chip that is intended to securely store the international mobile subscriber identity (IMSI) number and its related key, which are used to identify and authenticate subscribers on mobile telephony devices.
Click for more info
3FF
3FF (3rd Form Factor) is a very small SIM card, also known as micro-SIM, for use in small mobile device.
Click for more info
EAC
Extended Access Control. A mechanism enhancing the security of ePassports whereby only authorized inspection systems can read biometric data.
Click for more info
GSM
Global System for Mobile Communications. A European standard for digital cellular phones that has now been widely adopted throughout the world.
PDA
Personal Digital Assistant. A mobile device that functions as a personal information manager, often with the ability to connect to the internet.
PIN
Personal Identification Number. A secret code required to confirm a user's identity.
BER
Bit Error Rate. A measure of received signal quality, the proportion of received bits which is decoded erroneously.
Click for more info
CID
Cell IDentifier. In LTE, an identifier of a particular cell, either a Physical CID or a Global CID. Up to 504 Physical CIDs are available.
CRC
Cyclic Redundancy Check. An error detecting code appended to a block of data to be transmitted. The value of the CRC is calculated only from the block of data itself. The length of the CRC determines the number of errors which can be detected in the block of data on reception. A CRC is not able to correct errors or determine which bits are erroneous.
Click for more info
IMS
Internet Protocol Multimedia Subsystem. An architectural framework for delivering Internet Protocol (IP) multimedia services via UTRAN and E- UTRAN. See 3GPP TS23.228 and TS23.406.
LAI
Location Area Identity. The LAI is composed of the Mobile Country Code (MCC), the Mobile Network Code (MNC) and the Location Area Code (LAC). See 3GPP TS23.003 Section 4.1.
MNC
Mobile Network Code. In conjunction with the Mobile Country Code (MCC), the MNC uniquely identifies a mobile network operator/carrier. In LTE it is used in the construction of network entity related identities such as the E- UTRAN Cell Global Identifier (ECGI), the Global eNodeB Identifier, and the Tracking Area Identity (TAI). See 3GPP TS23.003 Section 2.2 and TS36.300 Section 8.2.
NDS
Network Domain Security. A security architecture for network domain Internet Protocol (IP) based control planes, which is applied to NDS/IP-networks (i.e. 3GPP and fixed broadband networks) to provide security in the Core Network (CN). See 3GPP TS33.210.
RAC
Radio Admission Control. The RAC function is located in the eNodeB and controls admission or rejection of new radio bearer establishment requests. The goal of RAC is to maximize radio resource utilization while ensuring that the required Quality of Service (QoS) is achieved for sessions which are already established. RAC can take into account the overall resource situation in E- UTRAN, the QoS requirements, the priority levels, the provided QoS of in- progress sessions and the QoS requirements of new radio bearer requests. See 3GPP TS36.300, Section 16.1.2.
RAN
Radio Access Network. A RAN consists of the ground-based infrastructure required for delivery of communication between UEs and the Core Network (CN). In LTE, the RAN consists of one or more base stations (i.e. eNodeBs). Examples of other RANs are UMTS, TD-SCDMA, GSM, CDMA2000 and WiMAX.
RAT
Radio Access Technology. The RAT is the type of radio technology used in a Radio Access Network (RAN) to access the Core Network (CN), e.g. UMTS, GSM, CDMA2000, WiMAX.
DM
Device Management: Management of mobile phone configuration, updates and other managed objects of mobile devices over the entire life-cycle as defined by OMA DM. DM is also used generically to describe all methods and activities associated with mobile device management.
Click for more info
IM
Using text on a mobile handset to communicate in real time
IP
Internet Protocol. A protocol for communicating data accross a network
Click for more info
OS
Operating System. Software that runs on computers and other smart devices and that manages the way they function.
SE
Secure Element. A secure and personalised physical component added to a system to manage users rights and to host secure apps. SE typically consist of a Silicon Chip, a secure Operating System, application software and a secure protocol to communicate to the device. SE can be a removable device (such as UICC or µSD for mobile devices or MIM for M2M connected machines). SE can also be components inside the system.
BS
Base Station. The entity in a radio access network responsible for radio trans- mission and reception in one or more cells to and from the UE. In LTE the BS is known as the eNodeB.
Click for more info
HE
Home Environment. The HE of a subscriber is responsible for the overall pro- vision and control of the personal service environment to the subscriber.Â
HO
HandOver. HO is a procedure by which a mobile terminal changes serving cells (within the same frequency or on different frequencies or even on different Radio Access Technologies (RAT)). See 3GPP TS36.133.
PS
Packet Switched. In PS communication each data packet is labelled with the destination address and routed over a shared transmission resource. In contrast with Circuit Switching (CS) where dedicated transmission resources are re- served between network nodes to deliver a reliable transmission rate and delay, in a PS connection the transmission rate and delay may vary depending on the traffic load and the medium capacity, with packets being buffered if necessary.
UE
User Equipment. The mobile unit which allows a user to access network services, connecting to the UTRAN or E-UTRAN via the radio interface. A UE can be subdivided into a Universal Integrated Circuit Card (UICC) and a Mo- bile Equipment (ME). See 3GPP TS21.905 Section 3.
SIM
A subscriber identity module or subscriber identification module (SIM) is an integrated circuit chip that is intended to securely store the international mobile subscriber identity (IMSI) number and its related key, which are used to identify and authenticate subscribers on mobile telephony devices.
Click for more info