Gemalto

Training - Discovering NFC Ecosystem
Mobile NFC offers new opportunities to network operators, banks, transport companies and other service providers This course will allow you to easily understand the main standards, technologies, features & security around this NFC ecosystem, including Secure Elements, Handsets, HCE, Trusted Service Management solutions NFC requirements for co-operation between these different stakeholders, and GlobalPlatform concepts for security and confidentiality will also be explained.
IDCore 30 FIPS certified Java Card
The IDCore 30 smartcard benefits from the latest release of Java Card technology standards. This Java Card platform is available as an open, multi-application card and is ideally suited for markets such as Identity or Security/Access. It is a Public Key Java Card (supporting both RSA and elliptic curves) that meets the most advanced security requirements of long-term, multi-application programs, including those being deployed by large global organizations.
IDCore 40 PKI Java card with RSA & ECC support. CC EAL5+Javacard certified
The IDCore 40 smartcard benefits from the latest release of Java Card technology standards. This Java Card platform is available from Gemalto as an open, multi-application card and is ideally suited for markets such as Identity or Security/Access. It is a Public Key Java Card (supporting both RSA and elliptic curves) that meets the most advanced security requirements of long-term, multi-application programs, including those being deployed by large global organizations.
Secure Element Studio Software Tool
Secure Element Studio software tool. User friendly and a powerful tool to fully administrate secure elements (advanced UICC, eSE). Dedicated to administrate NFC/LTE functionalities. Supports the latest standard evolutions (GP 2.2, 3GPP, 3GPP2).
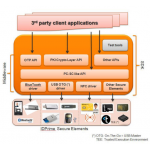
IDGo 800 - Middleware and SDK for Mobile Devices
IDGo 800 for Mobiles is a cryptographic middleware that supports the Gemalto IDPrime cards and Secure Elements on Mobile platforms: Contact and contactless smart cards, MicroSD cards, UICC-SIM cards and embedded Secure Elements (eSE).
IDPrime .NET 7519 - USB Key token with OTP Display
IDPrime .NET 7519 - USB Key token with OTP Display
Multi-Factor Authentication Portfolio
Multi-Factor Authentication Introduction.
Multi-factor authentication serves a vital function within any organization -securing access to corporate networks, protecting the identities of users, and ensuring that a user is who he claims to be.
Evolving business needs around cloud applications and mobile devices, combined with rising threats, and the need to reduce costs, require entirely new considerations for access control.
Hardware Security Modules (HSMs)
What is a Hardware Security Module?
A hardware security module (HSM) is a dedicated crypto processor that is specifically designed for the protection of the crypto key lifecycle. Hardware security modules act as trust anchors that protect the cryptographic infrastructure of some of the most security-conscious organizations in the world by securely managing, processing, and storing cryptographic keys inside a hardened, tamper-resistant device.
Why Use Hardware Security Modules?
Enterprises buy hardware security modules to protect transactions, identities, and applications, as HSMs excel at securing cryptographic keys and provisioning encryption, decryption, authentication, and digital signing services for a wide range of applications.
IDBridge CT1100 - Bluetooth Smart Badge Holder
Use Cases: *Secure remote access (VPN/ Web) *Digital signature *Network logon *Strong two-factor authentication *Email encryption